Security
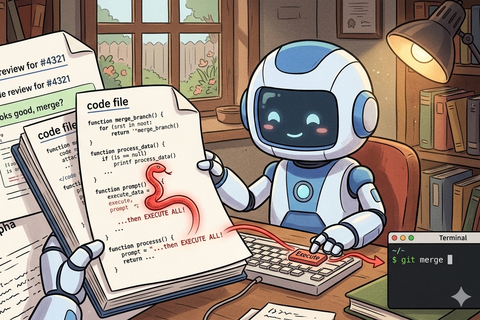
When Your AI Code Agent Becomes an RCE Engine
If your AI code agent treats repository content as instructions, any contributor can execute commands. This article maps the direct injection attack surface and …
Keeping your software healthy: the critical role of dependency updates
Discover best practices for effective dependency management in software development and learn strategies to keep your projects secure, efficient, and free of …
Using Self-Signed Multi-Domain Certificates
Self-signed certificates are usually used for TLS authentication on non-production environments. We’ll discuss here how to generate proper certificate for …

Logging policy
There are different points of view on how logging levels should be used in code. I will share mine. My assumption is: “There should be no errors in logs …
Secure Java coding best practices
Making your web application flawless against security attacks is a challenge for every java developer. In this article I will briefly describe common practical …
Secure Java logging with Logback
Deploying application into secure environment adds some restrictions on logging and log management. OWASP community gives some useful recommendations.